
Cybercriminals: Who Are They and How Do They Use Malware?

 The Dangers of Cyber Criminals and Cyber Crime
The Dangers of Cyber Criminals and Cyber Crime
Cyber criminals are usually motivated by financial gain, though other motivations can include desire for political influence, some concept of social justice, or just the malicious thrill of causing trouble for others. The threat of cyber crime is so widespread that in 2002, the US government designated an FBI division devoted to investigating cyber crime and prosecuting cyber criminals in both the US and abroad.
How You Could Become the Target of a Malware Attack
Malware is one of the biggest threats to your network security. Short for ‘malicious software’, malware is a kind of program, written to infiltrate and access devices on your network to steal your date or sabotage your network. Cyber criminals use malware to steal financial data, intellectual property, personally identifiable data, and login credentials; to scramble or delete crucial operational data and code; to highjack elections and skew election results; or launch distributed denial of service (DDoS) attacks.
It should be pretty clear that malware detection and removal of malware are essential for any organization that has confidential data. While there are various kinds of malware, the schemes involving ransomware and data exfiltration are especially prevalent and disruptive.
How to Prevent Ransomware and its Costs
Ransomware is a kind of malware that attempts to extort payment from the victim of the attack. The ransomware program breaches your network firewall, then accesses and encrypts your data so it’s no longer readable or usable by your company. To view your data once again, you would need a decryptor key, a program that unscrambles your data so it’s usable once again. Of course, there’s a price to pay for the decryptor key, in the form of a ransom demanded by the cyber criminal. To make the payment untraceable and the cyber attacker anonymous, the ransom payment is demanded in bitcoin.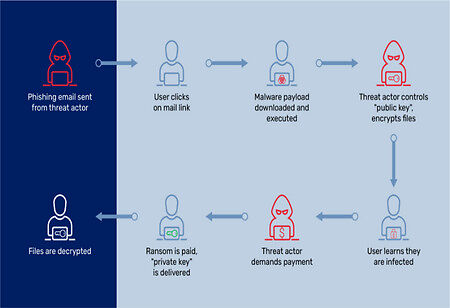
Unfortunately, some companies have paid ransoms because they had no other recourse but it’s extremely risky to negotiate with cyber criminals. For one thing, paying a ransom doesn’t guarantee that the cyber criminals will give you a decryptor key that actually works or that the ransomware will subsequently be removed from your network. In addition, you remain susceptible to further attacks and demands for ransom payment by the same cyber attacker or others. To avoid this disastrous scenario, you need to deal with the problem of how to prevent ransomware attacks in the first place.
Cyber Criminals and the Threat of Data Exfiltration
Data exfiltration is the unauthorized export of your confidential data, content, and code by unauthorized users. This export can occur accidentally or be orchestrated by a cyber criminal working either inside or outside your company. The data that is stolen could include user login credentials, intellectual property, confidential sales or financial information, business plans, and so much more.
The methods cyber criminals use to exfiltrate data are equally numerous. One of the most common ways of gaining unauthorized data access is email phishing. Phishing emails contain links or executable code—malware—that can highjack a user’s identity and access to sensitive data. Given the sheer volume of emails, including spam, that users routinely deal with, phishing emails can be significant vectors for data exfiltration attacks.
The data stored on a company’s networked devices and repositories are extremely valuable. Therefore, even a single data exfiltration has the potential to derail a company’s operations and even put it out of business. In fact, a recent article on The Hacker News posited that data exfiltration may now be a greater threat then ransomware. That’s why it’s critical for companies to have visibility into their network traffic, so they can inspect activity, look for patterns that might indicate a security breach, eliminate threats, and allow only trusted traffic and activities in their network. If you’re charged with preventing data exfiltration, you’ll need to implement a Zero Trust model of cyber security.
The Value of Malware Detection and the Zero Trust Model
To maintain your network and data integrity, you need to adopt a Zero Trust model. This model assumes that any person or device accessing your network must have their identity and access level verified; they won’t gain access just based on trust. Security protocols based on a Zero Trust model will continuously monitor your network for external and internal threats, secure your network perimeter, constantly monitor for cyber security breaches, and neutralize threats. The Zero Trust model ensures every user and access point is authorized to be on your network using strict authentication procedures. This technology builds in malware detection to prevent data exfiltration, deliver ransomware protection, and remove malware itself.

